Integrity Verification Assets
Francesco Vaccaro (Politecnico di Torino)
21/04/2026
Introduction
The transition to Post-Quantum Cryptography (PQC) is becoming a fundamental requirement for modern digital infrastructures [1]. Within the QUBIP project, several building blocks are being progressively adapted to withstand the threat posed by future quantum computers. Among these, Integrity Verification mechanisms play a crucial role in establishing trust in distributed systems, particularly in cloud, edge, and Internet of Things (IoT) environments.
In the previous QUBIP blog post on Integrity Verification, the foundations of secure boot, measured boot, and remote attestation were introduced as key techniques to ensure that systems execute only trusted software and maintain a verifiable operational state. This work extends that discussion by focusing on the implementation of concrete assets that enable quantum-safe integrity verification in real-world deployments.
This blog post summarises our recent research activity on the integration of post-quantum digital signatures into the Keylime [2] remote attestation framework, providing a practical example of how integrity verification mechanisms can be adapted to the post-quantum era.
Background
Integrity verification relies on cryptographic primitives to guarantee the authenticity and integrity of system measurements. Traditional public-key cryptographic algorithms such as RSA and Elliptic Curve Cryptography are widely used today, but they are vulnerable to attacks from sufficiently powerful quantum computers. Post-Quantum Cryptography introduces new algorithms designed to remain secure even in the presence of quantum adversaries. Among the various families of PQC algorithms, lattice-based digital signatures have emerged as strong candidates due to their efficiency and security guarantees. In particular, the ML-DSA algorithm [3], standardised by the National Institute of Standards and Technology (NIST), provides a robust foundation for implementing quantum-safe remote attestation. Trusted Computing technologies provide the architectural basis for integrity verification. The Trusted Platform Module (TPM) [4] acts as a hardware Root of Trust, securely storing cryptographic keys and generating signed integrity reports. In addition, Trusted Execution Environments (TEEs) provide hardware-enforced isolation for sensitive operations, ensuring that critical security components remain protected from compromise.
Architecture
The architecture developed in this work targets resource-constrained IoT devices while maintaining strong security guarantees. The core component is a firmware-based Trusted Platform Module (fTPM) [5] deployed inside a TEE based on ARM TrustZone technology. The system integrates the following main components:
- A Trusted Execution Environment hosting the firmware TPM [6];
- The Keylime remote attestation agent running in the normal operating system [7];
- The Integrity Measurement Architecture (IMA) module for runtime measurement collection [8];
- A post-quantum digital signature engine implementing the ML-DSA algorithm.
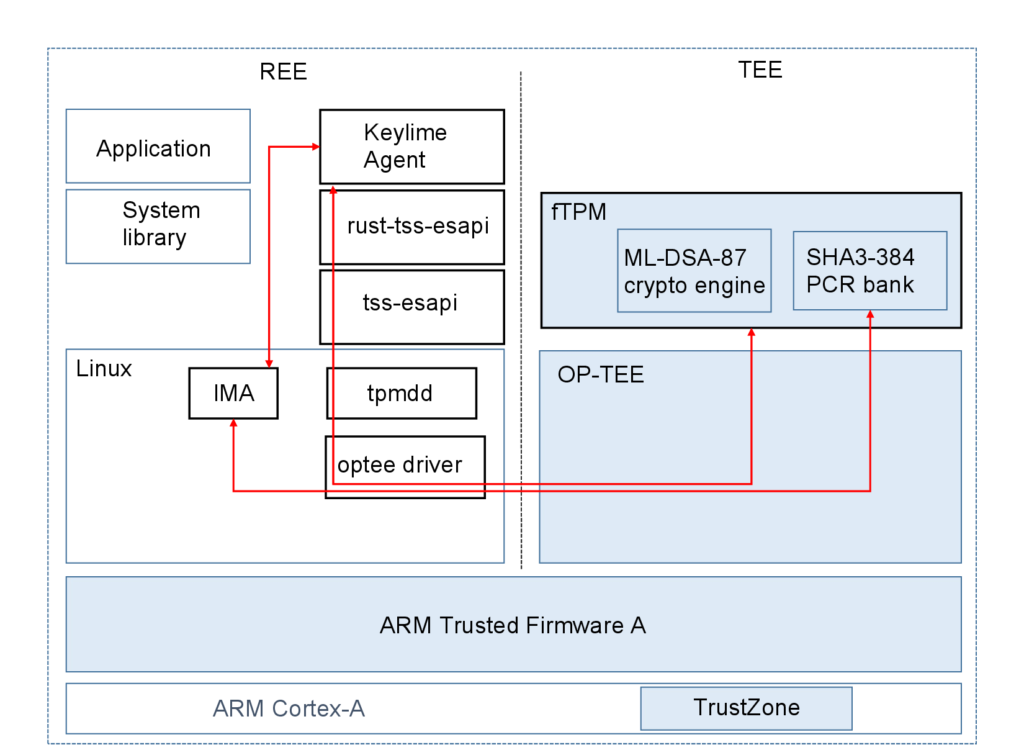
Figure 1: Post-quantum remote attestation architecture integrating Keylime, OP-TEE, and a firmware TPM.
The remote attestation process operates continuously, enabling timely detection of system compromises. Measurements collected during system boot and runtime are stored inside Platform Configuration Registers (PCRs) and signed by the TPM using post-quantum cryptographic keys.
TPM Software Stack and ESAPI Integration
A crucial component enabling post-quantum cryptographic operations into the Keylime framework is the Trusted Platform Module Software Stack (TSS). The TSS provides a standardised interface that abstracts the low-level details of TPM communication and exposes a set of APIs that can be used by applications and security services.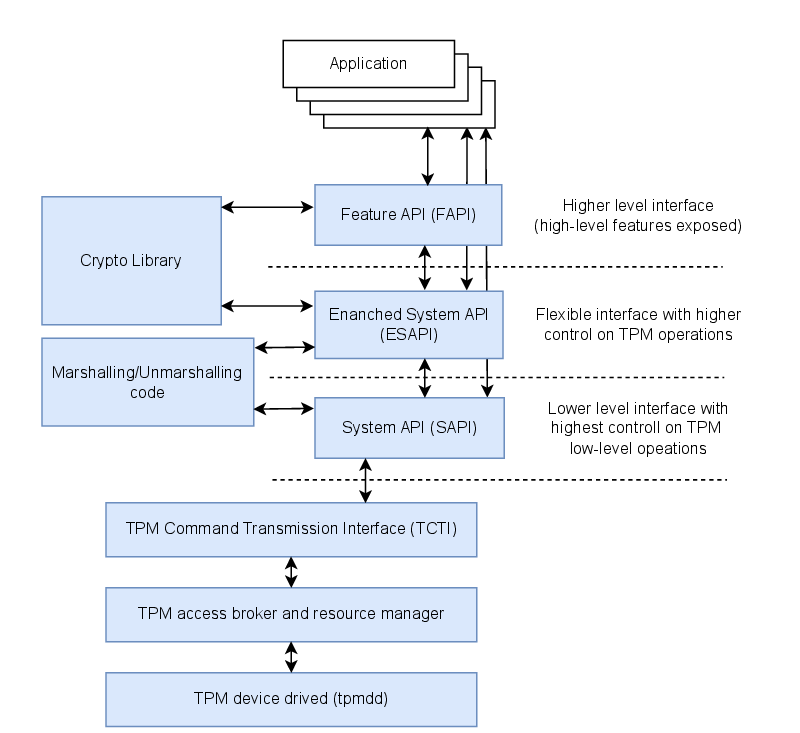
Figure 2: Logical structure of the TPM Software Stack (TSS) and its main API layers.
Among the available interfaces, the Enhanced System API (ESAPI) plays a central role in our implementation. ESAPI provides a flexible programming abstraction that balances ease of use and fine-grained control over TPM operations. The Keylime agent used in our implementation is written in Rust. To interact with the TPM, we leveraged the rust-tss-esapi wrapper [9], an open-source Rust interface that provides safe bindings to the ESAPI layer. In our implementation, the wrapper was extended to support post-quantum operations exposed by the modified ESAPI layer, including support for ML-DSA-based key creation and quote generation.
Results
To evaluate the feasibility of the proposed solution, we implemented a prototype platform based on an emulated ARM system. The platform includes a firmware TPM supporting the ML-DSA digital signature algorithm. Experimental results show that integrating post-quantum cryptography does not introduce significant performance overhead in key generation or remote attestation operations. In particular, the time required to generate attestation evidence remains comparable to traditional algorithms such as RSA and ECDSA.
The primary impact of adopting post-quantum algorithms is related to the increased size of cryptographic keys and signatures. While this introduces additional memory requirements, the performance characteristics remain compatible with typical IoT deployment scenarios. These results confirm that quantum-safe integrity verification can be implemented today using software-based solutions, paving the way for future hardware implementations.
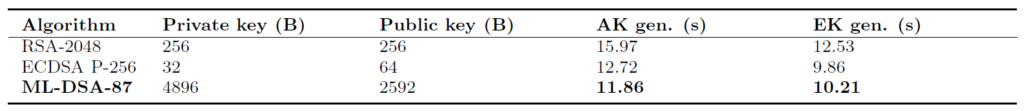 Table 1: Time necessary for key generation (Attestation Key (AK) and Endorsment Key (EK)) with the firmware Trusted Platform Module (fTPM) supported algorithms.
Table 1: Time necessary for key generation (Attestation Key (AK) and Endorsment Key (EK)) with the firmware Trusted Platform Module (fTPM) supported algorithms.
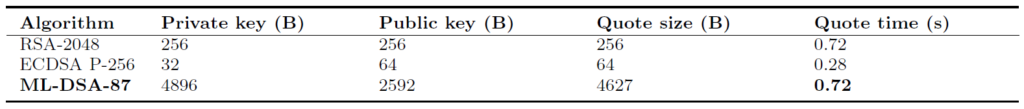 Table 2: Time necessary for quote generation with the fTPM supported algorithms.
Table 2: Time necessary for quote generation with the fTPM supported algorithms.
Conclusions and Future Work
The transition to post-quantum cryptography is a long-term process that requires gradual adaptation of existing security infrastructures. Integrity verification mechanisms are among the most critical components that must evolve to maintain trust in computing systems.
In this work, we demonstrated the integration of a post-quantum digital signature algorithm into the Keylime remote attestation framework, showing that quantum-safe integrity verification can be achieved without significant performance penalties.
Future work will focus on extending support to additional post-quantum algorithms, optimising memory usage for constrained devices, and validating the solution on real hardware platforms. These activities will contribute to the broader goal of establishing secure and resilient infrastructure capable of operating safely in the post-quantum era.