Integration of PQC in TLS Protocol for IoT Devices
M. C. Molteni, L. Nava, A. Gringiani, G. Greco (Security Pattern)
01/02/2024
With the advent of quantum computing, traditional cryptographic algorithms face an imminent threat of being compromised, necessitating the development and integration of post-quantum cryptographic solutions. In addition, in our modern world, security needs to be integrated into small embedded devices that surround us in our daily life (home automation, industry controllers, etc.) so it is very important that embedded low-power devices are secured with state-of-the-art cryptographic algorithms and protocols.
Symmetric and asymmetric cryptography are two fundamental concepts in the field of cryptography. Symmetric Cryptography uses a single secret key for both encryption and decryption and provides security by safely distributing and managing the secret key among communication parties. Symmetric algorithms can easily archive protection against post-quantum computers by using keys of 256 bits or higher. On the other hand, Asymmetric Cryptography uses a pair of keys: a public one (used for encryption) and a private one (used for decryption), the security of currently used asymmetric algorithms is based on the difficulty of solving mathematical problems. As these problems could be easily solved on a quantum computer running Shor’s algorithm, there is the necessity of finding quantum-safe alternatives. NIST (National Institute of Standards and Technology) in the post-quantum standardization process in 2022 [1] chose four valid post-quantum algorithms: Kyber for the Key encryption mechanism (based on lattice cryptography) and Dilithium, Falcon and SPHINCS+ (the first two based on lattice cryptography and the latter based on hash functions) to perform digital signature. They are starting to define them, respectively, as ML-KEM in FIPS 203, ML-DSA in FIPS 204, and SLH-DSA in FIPS 205 [2].
NIST, in the Special Publication 800-131A [3], defined three security levels (level 1, level 3, Level 5) that correspond to different levels of security strength for cryptographic algorithms. Level 1 provides a basic level of security, used for applications where the primary goal is to protect against casual threats. Level 3 provides a moderate level of security suitable for protecting sensitive information. Level 5 provides a high level of security and is suitable for protecting highly sensitive information and systems.
Transport Layer Security (TLS) is the de facto standard for secure communication on the Internet.
The core of the security provided by the TLS is in the Handshake protocol, used for authentication, negotiation of the used cryptographic primitives, and the establishment of session keys. The handshake protocol can use either RSA or Diffie Hellman in the key exchange, and RSA and DSA as well as the elliptic curve for digital signatures. Those algorithms are based on the integer factorization problem (RSA), the discrete logarithm problem (DH and DSA) and the elliptic-curve discrete logarithm problem (ECDH and ECDSA). All of these problems could be easily solved on a sufficiently powerful quantum computer running Shor’s algorithm [4][5].
Implementing post-quantum algorithms in embedded systems is challenging for a lot of reasons. Firstly, the memory that we have in an embedded device may be small and does not allow us to use post-quantum algorithms efficiently. Moreover, some post-quantum algorithms necessitate larger key sizes for equivalent security compared to classical algorithms, therefore storing and managing these larger keys on embedded devices with restricted storage capacity can be challenging. Lastly, the increased computational requirements could not be satisfied by embedded devices operating on battery power (see as introduction [6]).
To address those problems, two ways can be followed:
- Lightweight cryptography, that involves creating versions of post-quantum cryptographic algorithms that are optimized for efficiency and designed to operate within the constraints of embedded devices.
- Hybrid cryptography, that involves a combination of both classical cryptographic algorithms and post-quantum algorithms. This enables a gradual transition, allowing compatibility with existing systems, while incorporating the benefits of post-quantum security.
The long-term benefits of integrating post-quantum solutions into the TLS protocol for embedded devices extend beyond immediate security improvements. They encompass adaptability to future threats, resilience against quantum computing advancements, and the establishment of a trustworthy and standardized environment for interconnected systems. This strategic integration not only safeguards against current risks but also positions embedded devices to thrive in the evolving landscape of cybersecurity threats.
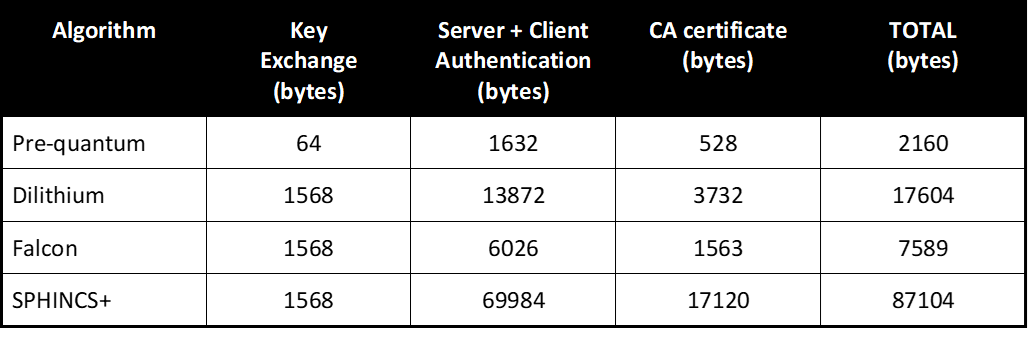
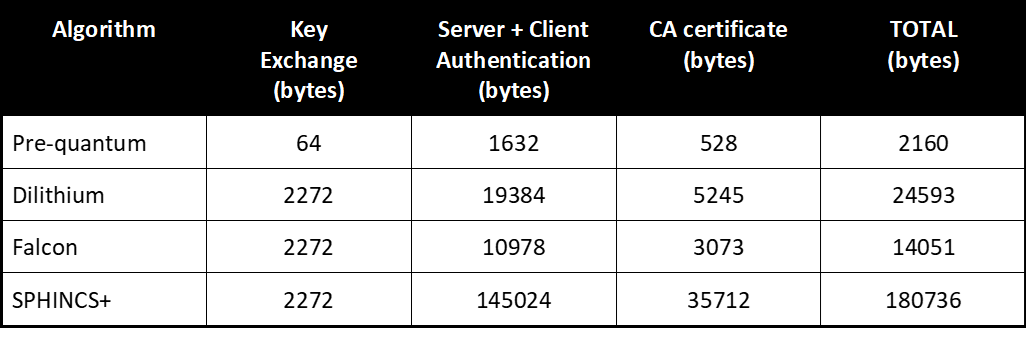
Performance analysis of post-quantum TLS in an emulated network
For a better overview on the performance of post-quantum algorithms we can summarize the results reported in [7] in the following tables showing the communication sizes for the handshakes depending on the algorithm chosen. In this work, PQ algorithms in TLS1.3 are implemented using MbedTLS [8].
LEVEL 1
LEVEL 3
LEVEL 5
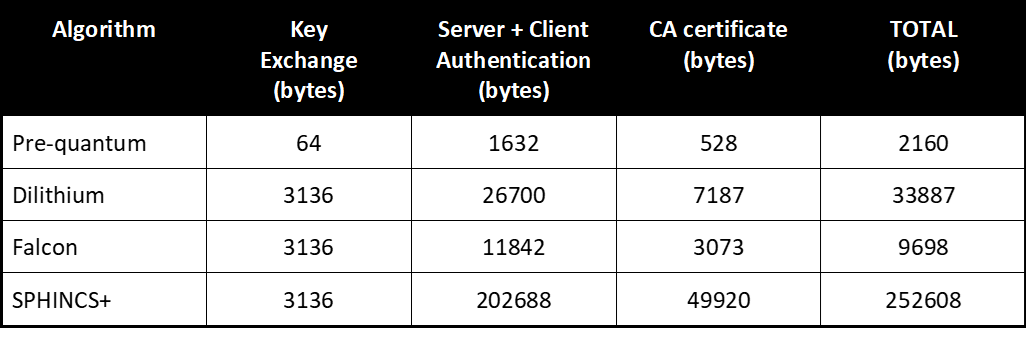
We can see that over the security level 1, 3, 5, Kyber (for Key encryption) and Dilithium offer reasonable performance.
The size of Dilithium does affect the handshake times significantly at levels 3 and 5, due to these instances exceeding the initial congestion window size.
Falcon offers comparable or better performance, and its public keys and signatures are the shortest. However, using Falcon for online signatures is not an option, due to its requirement of constant-time 64-bit floating-point arithmetic for signing.
Using SPHINCS+ does not seem very attractive for TLS 1.3: the scheme significantly affects the handshake performance both in computation time and in size of signatures. However, this algorithm has been chosen because it is based on hash cryptography, which is a consolidated field of study, so it allows a conservative choice unrelated to lattice-based cryptography.