CCIPS & PQC/QKD for Quantum-Resilient Networking
M. Elorza, A. Pastor (TID), R. Brito, R. Querol (UPM)
19/03/2026
Introduction
As the telecommunications industry moves towards Post-Quantum Cryptography (PQC), one of the main challenges is how to protect secure communications while preserving compatibility with current infrastructures and operational models and avoid single-technology lock-in. In this context, traditional key exchange mechanisms such as IKEv2 raise important concerns due to their expected vulnerability in a future quantum-threat scenario [1]. The QUBIP project addresses this challenge by exploring a quantum-resilient security architecture designed for virtualized and cloud-native telecom environments.
At the core of this innovation are two key components: the Centrally Controlled IPsec (CCIPS) framework and the Hybridization Module. Together, they enable the establishment of secure IPsec tunnels without relying on IKE-based negotiation, while supporting the coordinated use of PQC, Quantum Key Distribution (QKD), and, when needed, classical cryptographic mechanisms within a unified and programmable security model. The result is a scalable, standards-based solution designed for Kubernetes clusters and software-defined infrastructures.
System Architecture and Operational Workflow
The QUBIP architecture is designed to securely interconnect distributed, virtualized environments across potentially untrusted networks. Rather than focusing on intra-cluster communication only, the architecture enables secure connectivity between independent domains, edge locations, or data centers. To achieve this, it combines centralized control, programmable networking, and hybrid quantum-safe cryptography to establish secure tunnels between remote endpoints. In this way, secure communication can be dynamically orchestrated across heterogeneous infrastructures while preserving confidentiality, integrity, and a transition path towards more future-proof cryptographic protection.
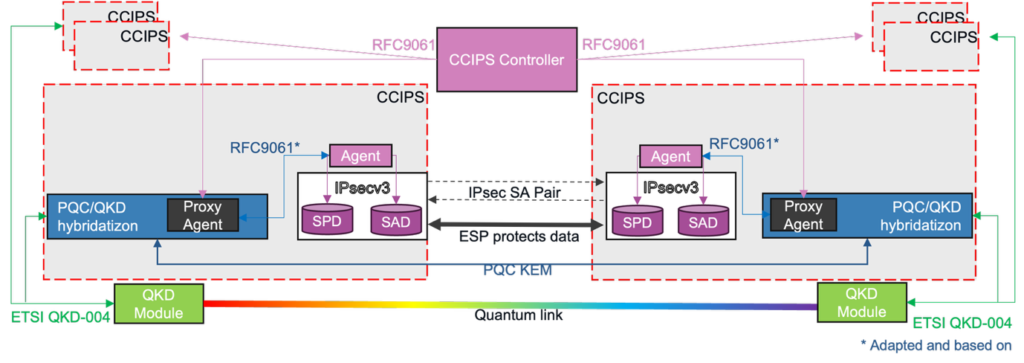
The CCIPS Controller plays a central role in the system. Instead of using distributed IKE negotiations, it manages IPsec tunnel establishment in a centralized manner following RFC 9061 [2]. In this way, Security Association Database (SAD), Security Policy Database (SPD) parameters, and related tunnel configuration can be generated and distributed to the worker nodes through structured control messages. This controller-driven approach removes the dependency on IKEv2 and enables programmable and coordinated tunnel management.
On each Worker Node, a CCIPS Agent, a Proxy Agent, and the Hybridization Module are deployed. The Proxy Agent receives the service and security parameters generated by the CCIPS Controller and acts as the intermediary between the controller-driven IPsec logic and the lower cryptographic layer. In our approach, the Proxy Agent is in charge of processing two differentiated sets of information. On the one hand, it receives the parameters associated with the secure service itself, such as the protected connectivity relationship, the IPsec mode to be applied, or the traffic domains that must be protected. On the other, it receives the information required to define the behavior of the Hybridization Modules located at the communicating endpoints. In this way, the Proxy Agent plays a key role in translating service-level requirements into cryptographic and operational actions.
The Hybridization Module, named after its ability to apply explicit key-hybridization mechanisms to the cryptographic material obtained from different sources, is responsible for integrating heterogeneous cryptographic sources under a common operational model. This design provides crypto‑agility, allowing the system to adapt the cryptographic mix over time as new post‑quantum schemes are standardized or existing ones are deprecated. In particular, it can obtain quantum keys from external QKD systems through the ETSI GS QKD 004 interface [3], while also incorporating post-quantum shared material derived from PQC mechanisms such as ML-KEM-512 [4]. When required by the selected procedure, Hybridization Modules at remote endpoints may also coordinate with each other in order to support PQC- or classical-based operations that require endpoint-to-endpoint interaction. In particular, the module is not limited to collecting QKD-, PQC-, or classical-derived material independently, but can also combine them through hybridization procedures such as XOR-based composition or HMAC-based constructions. This capability is especially relevant in transition scenarios, where different cryptographic technologies may provide complementary properties and where the resulting secure service benefits from a coordinated use of heterogeneous key sources. In this way, the module acts not only as an integration point, but also as the functional element that materializes cryptographic hybridization within the architecture. Once the required material has been obtained or combined, it is returned to the Proxy Agent, which uses it to complete the corresponding tunnel provisioning process.
By integrating QKD- and PQC- derived material, and by supporting explicit hybridization procedures over heterogeneous cryptographic inputs, the Hybridization Module contributes to strengthening tunnel protection against both present-day and future threats. At the same time, the overall design remains hardware-agnostic and containerized, which facilitates deployment in cloud-native environments while preserving interoperability with external QKD systems.
Conclusions
The CCIPS framework and the Hybridization Module developed in QUBIP represent a significant step toward quantum-resilient networking for telecom operators and cloud-native infrastructures. By removing dependency on IKE-based key exchange and adopting a controller-driven IPsec model, the architecture aligns security with modern SDN paradigms.
At the same time, the coordinated use of QKD, PQC, and hybridization mechanisms provides a more flexible and resilient approach to secure tunnel provisioning. Through centralized orchestration, standards-based interfaces, and containerized deployment, QUBIP shows that the transition to quantum-safe networking can be integrated into programmable and virtualized environments in a realistic and operationally meaningful way.
More broadly, this work highlights that the post-quantum transition is not only a matter of adopting new cryptographic algorithms, but also of designing architectures capable of coordinating heterogeneous security technologies under a common operational framework. This coordinated approach is inherently resilient and deliberately avoids single‑technology lock‑in, reducing the operational and security risk of depending solely on PQC or any other individual mechanism.
As future work, the architecture can be further extended with complementary mechanisms such as attestation-aware responses, refined coordination between remote Hybridization Modules, and validation in increasingly realistic telecom and cloud-native deployment scenarios. In this sense, QUBIP contributes to moving quantum-safe networking from theoretical promise towards deployable architectural practice.
References
| [1] NIST Post-Quantum Cryptography Standardization Project, [Online]. Available: https://csrc.nist.gov/projects/post-quantum-cryptography |
| [2] RFC 9061 – A YANG Data Model for IPsec Flow Protection Based on Software-Defined Networking (SDN), [Online]. Available: https://datatracker.ietf.org/doc/rfc9061/ |
| [3] ETSI GS QKD 004, [Online]. Available: https://www.etsi.org/deliver/etsi_gs/QKD/001_099/004/02.01.01_60/gs_qkd004v020101p.pdf |
| [4] NIST FIPS 203 – Module-Lattice-Based Key-Encapsulation Mechanism Standard, [Online]. Available: https://csrc.nist.gov/pubs/fips/203/final |